Negotiate Scholarship
Negotiate Scholarship - No matching host key type found. No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times Technically kerberos is the technological successor to ntlm. Iana has this angry remark about negotiate: But you can use either to authenticate against a windows domain/server. Microsoft said they were no longer supporting msonline back in march of 2024. I get the following error when using git: $ git pull unable to negotiate with 172.16.42.42 port 22: I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. I don't know what you mean by authenticate protocol but negotiate is kerberos authentication, if supported, and fallback to ntlm if not. I get the following error when using git: The authentication header received from the server was 'ntlm' asked 12 years, 8 months. Technically kerberos is the technological successor to ntlm. Started noticing the same thing on friday. In my.net 7 project, i have my authentication and authorization configured like the following: Microsoft said they were no longer supporting msonline back in march of 2024. No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times But you can use either to authenticate against a windows domain/server. $ git pull unable to negotiate with 172.16.42.42 port 22: I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. But you can use either to authenticate against a windows domain/server. I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times. I don't know what you mean by authenticate protocol but negotiate is kerberos authentication, if supported, and fallback to ntlm if not. I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. According to this blog post, azure api management. No matching host key type found. Iana has this angry remark about negotiate: Microsoft said they were no longer supporting msonline back in march of 2024. I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. Started noticing the same. $ git pull unable to negotiate with 172.16.42.42 port 22: The authentication header received from the server was 'ntlm' asked 12 years, 8 months. In my.net 7 project, i have my authentication and authorization configured like the following: No matching host key type found. Seems like they have finally pulled the plug. According to this blog post, azure api management should default to tls 1.2 if negotiate client certificate is enabled, since this is not allowed in tls 1.3. The authentication header received from the server was 'ntlm' asked 12 years, 8 months. No matching host key type found. But you can use either to authenticate against a windows domain/server. Iana has. $ git pull unable to negotiate with 172.16.42.42 port 22: No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times According to this blog post, azure api management should default to tls 1.2 if negotiate client certificate is enabled, since this is not allowed in tls 1.3. Iana has this angry. I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. $ git pull unable to negotiate with 172.16.42.42 port 22: Microsoft said they were no longer supporting msonline back in march of 2024. No matching host key type found. According. No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times The authentication header received from the server was 'ntlm' asked 12 years, 8 months. According to this blog post, azure api management should default to tls 1.2 if negotiate client certificate is enabled, since this is not allowed in tls 1.3.. Technically kerberos is the technological successor to ntlm. No matching host key type found. Microsoft said they were no longer supporting msonline back in march of 2024. According to this blog post, azure api management should default to tls 1.2 if negotiate client certificate is enabled, since this is not allowed in tls 1.3. I am making progress, annonymousauthentication=true also. $ git pull unable to negotiate with 172.16.42.42 port 22: I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. Started noticing the same thing on friday. No matching host key type found. Iana has this angry remark about negotiate: Iana has this angry remark about negotiate: Technically kerberos is the technological successor to ntlm. $ git pull unable to negotiate with 172.16.42.42 port 22: Seems like they have finally pulled the plug. Started noticing the same thing on friday. In my.net 7 project, i have my authentication and authorization configured like the following: No valid credentials provided asked 2 years, 9 months ago modified 2 years, 8 months ago viewed 3k times I don't know what you mean by authenticate protocol but negotiate is kerberos authentication, if supported, and fallback to ntlm if not. I am making progress, annonymousauthentication=true also allows the server to pass to and use cookie if it fails at the server level, and form aspnet core i can challenge the. The authentication header received from the server was 'ntlm' asked 12 years, 8 months. But you can use either to authenticate against a windows domain/server. According to this blog post, azure api management should default to tls 1.2 if negotiate client certificate is enabled, since this is not allowed in tls 1.3.3 Tips to Negotiate for a Higher Scholarship 2aDays News
How to Negotiate Law School Scholarships? ScholarshipBasket
How to Negotiate Your MBA Scholarship Like a Pro Maximize Your
Law school scholarship offers (how to negotiate) YouTube
How to Negotiate Your Financial Aid Offer in 2025 ScholarshipOwl
How To Negotiate For Scholarships Scholarship Success Series
How to Negotiate a Scholarship Offer YouTube
How to Negotiate your Scholarship 100 Scholarship MBA MS US
How to Negotiate an MBA Scholarship (with Examples!)
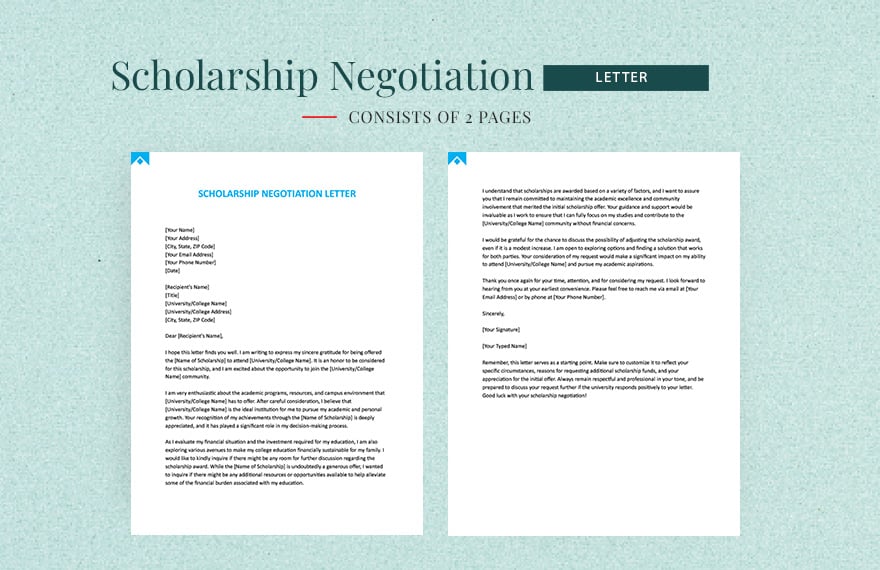
Scholarship Negotiation Letter in Word, Google Docs, Pages Download
I Get The Following Error When Using Git:
No Matching Host Key Type Found.
Microsoft Said They Were No Longer Supporting Msonline Back In March Of 2024.
Related Post: